Last updated on 19 August 2025
Important or Recent Updates
| Update | Date |
|---|---|
| New guide released | 06/06/2024 |
| Swapped the WireGuard container from LinuxServer to WG-Easy as it has a nice web UI! Also swapped the example Android Client to WG Tunnel. | 30/08/2024 |
| Amendments made to the bcrypt password element to ensure the hash is formatted correctly and amended the wording relating to the password being optional but recommended. | 04/11/2024 |
| Updated for the latest version apologies for the delay | 07/06/2025 |
| Swapped INIT_HOST to WG_HOST not sure why the other is not working as it was in the documentation for the latest version. | 23/06/2025 |
| My site is haunted – My changes from the November 2024 update seem to have decided to vanish! Restored them back! Also note IPv6 is disabled as it does not work on Synology (This was already in the compose but just adding the note) https://github.com/wg-easy/wg-easy/issues/2016 | 19/08/2025 |
What are we doing?
I already have a guide on how to set up Tailscale on your NAS for remote access. In the interest of choice and as I am currently using this method this is an alternative using WireGuard (WG-Easy).
This guide has a number of key steps. I will take you through each one, if you already followed some of my other VPN related guides you may be able to skip sections!
- Folder Setup
- DDNS Address
- TUN Script
- WireGuard Kernel Module
- Container Setup
- Client Setup
A note on Double NAT or CGNAT
Unfortunately more ISPs are moving to these methods of address allocation as the IPv4 address space is getting low on available addresses.
You can test if this is the case by checking the WAN IP on your Router/Modem settings and then comparing it to the one shown on portchecker.co. If they are different you are likely Double NAT and will either need to see if you can pay your ISP for a standard IPv4 address or use Tailscale (see my other guide) or Cloudflare Tunnels for access.
Let’s Begin
In this guide I will take you through the steps to things up and running in Container Manager. We will be using the new Projects (Docker Compose) feature as it will save you time vs manual setup using the normal UI.
Folder Setup
Let’s start by getting some folders set up for the containers to use. Open up File Station create the following.
/docker/projects/wg-easy-compose
/docker/wg-easy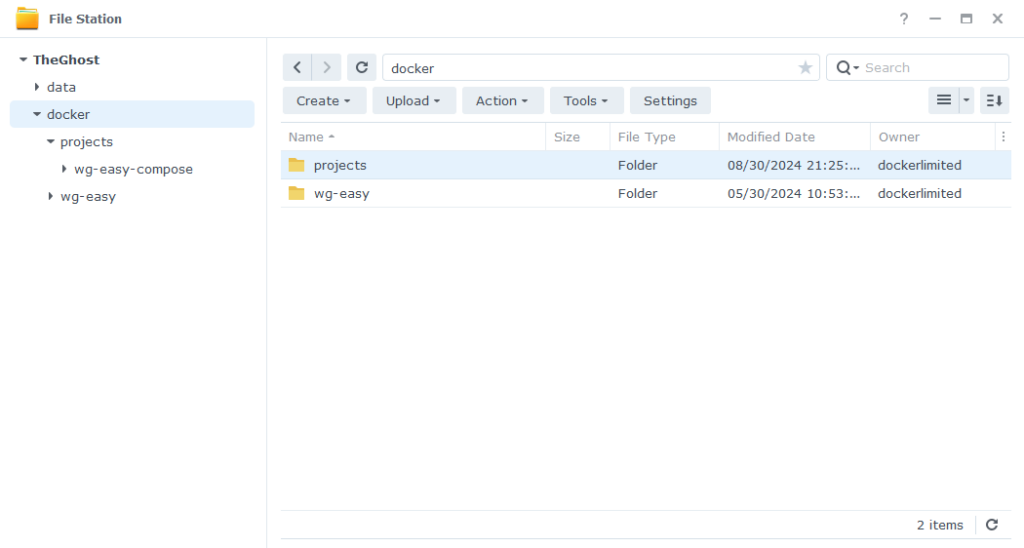
Next we need to set up a DDNS address in order to get connected.
DDNS and SSL
Before we start, make sure you have registered for a Synology Account as we are going to be using their DDNS service. https://account.synology.com/en-uk/register/ If you already have this set up move to the next step.
DDNS (Dynamic Domain Name System)
A DDNS address allows you to get external access to WireGuard via a domain provided by Synology, this is useful on home internet connections where your ISP will change your IP address on a regular basis. This will not put the NAS login screen on the internet by default as we won’t be opening the addition DSM ports on the router.
For some great hints and tips in relation to securing your NAS set Wundertechs recent guide.
In the DSM Control panel go to ‘External Access’ and then to the ‘DDNS’ tab
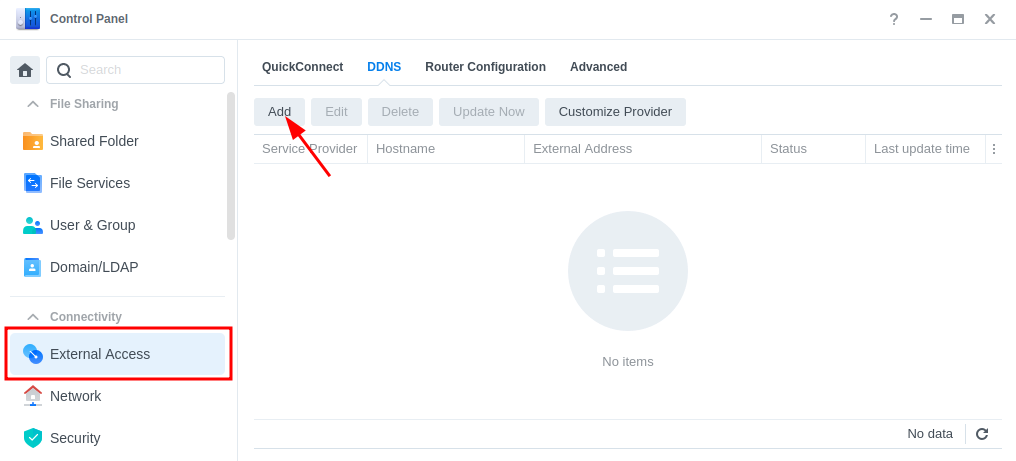
Click on ‘Add’, then fill out the following sections.
| Section | Value |
|---|---|
| Service Provider | Synology |
| Hostname | This will be the address used to identify your NAS so make it personal to you not specific to this guide. jellyseerr.synology.me = BAD myawesomenas.synology,me =GOOD |
| Email: | Log into your Synology account |
| External Address (IPv4) | This should be filled in automatically |
| External Address (IPv6) | This should be filled in automatically if your ISP is using IPv6 |
| Get a Cert from Let’s Encrypt | Tick this box |
| Enable Heartbeat | Tick this box |
Now press OK, DSM will apply your settings. It can take a few moments to set up and the DSM interface will refresh. You will likely receive a certificate error which you will need to accept to get back into DSM.
Setting up the TUN start up script
In order for the VPN connection to work we need to make sure the TUN Interface is available. In order to ensure it is available even after a reboot we will set up a small ‘script’.
Please note if you already have GlueTUN running you have already done this 🙂 so jump ahead
Open up Control Panel and then click on Task Scheduler
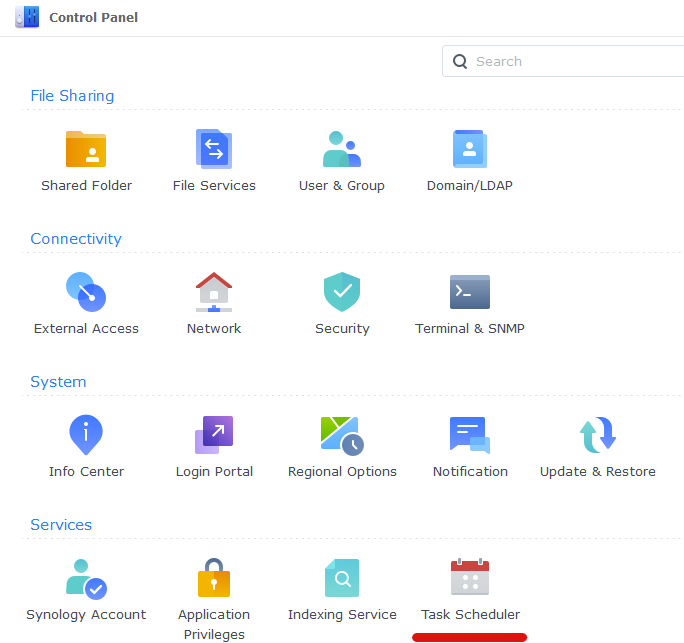
Next click on Create, Triggered Task then User Defined Script.
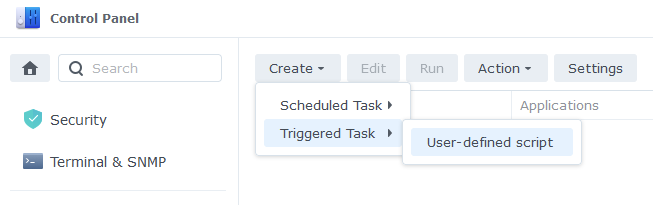
Enter the following:
| Section | Setting |
|---|---|
| Task: | VPNTUN |
| User: | root |
| Event: | Boot-up |
| Enabled | Tick |
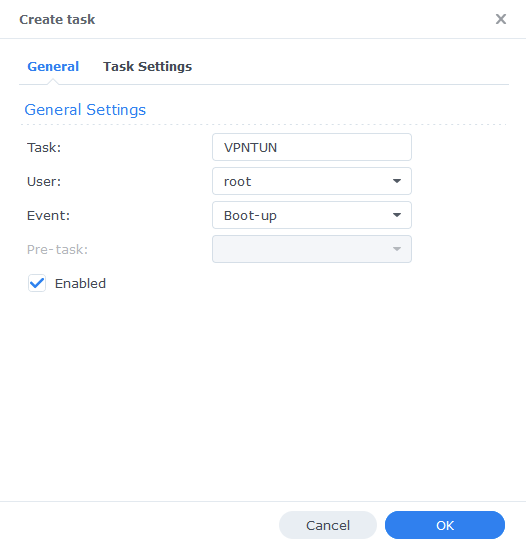
On the Task Settings tab copy and paste the code below in the ‘User-Defined script’ section. It will look like screenshot.
#!/bin/sh -e
insmod /lib/modules/tun.ko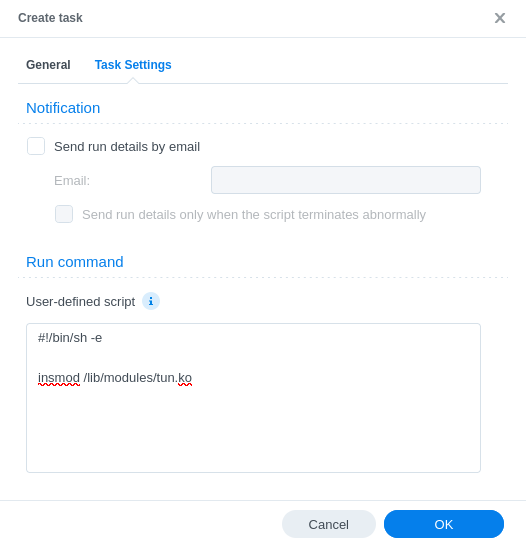
You can now press OK and agree to the warning message. Next run the script which will enable the TUN device.
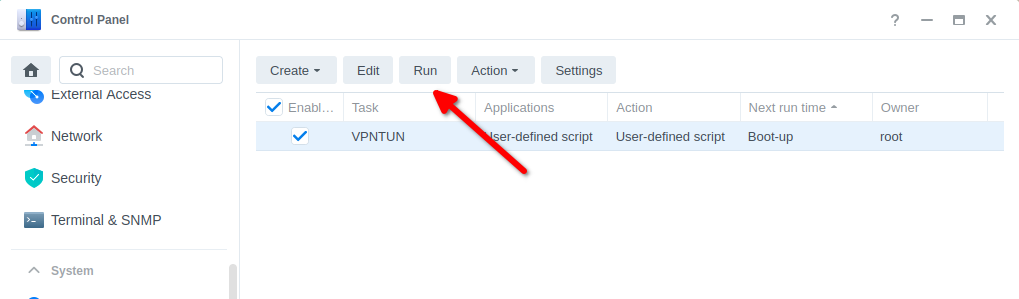
You can now move on to the next step.
WireGuard Kernel Module (Required)
As DSM uses an older Kernel that does not have the required WireGuard modules we need to load them separately.
BlackVoid.club have put together a Kernel Module for Synology which allows the lower level Kernel to perform WireGuard duties, make sure you drop them a thanks as this would not be possible without them!
While on first glances it looks like a long installation process the page details a number of methods. I recommend having a read taking note of warnings and also if you want to build your own module it tells you how.
The TLDR is below.
- Find your model of NAS under the correct DSM version section (If you are following this guide it will be 7.2) and download the pre compiled .spk file
- Head into Package Center and click ‘Manual Install’ on the top right and install the .spk file and untick the box to run after install
- Reboot
- SSH Into your NAS (Just like in the User Setup guide) and elevate yourself to root by typing
sudo -iand entering your password - Enter this command and press enter to start up the module
/var/packages/WireGuard/scripts/start
You should now be able to see the WireGuard package running in Package Center. Please note while I will try my best to support in relation to this module I may have to refer you on to BlackVoid if it is a specific technical issue.
On to the next part.
Container Manager
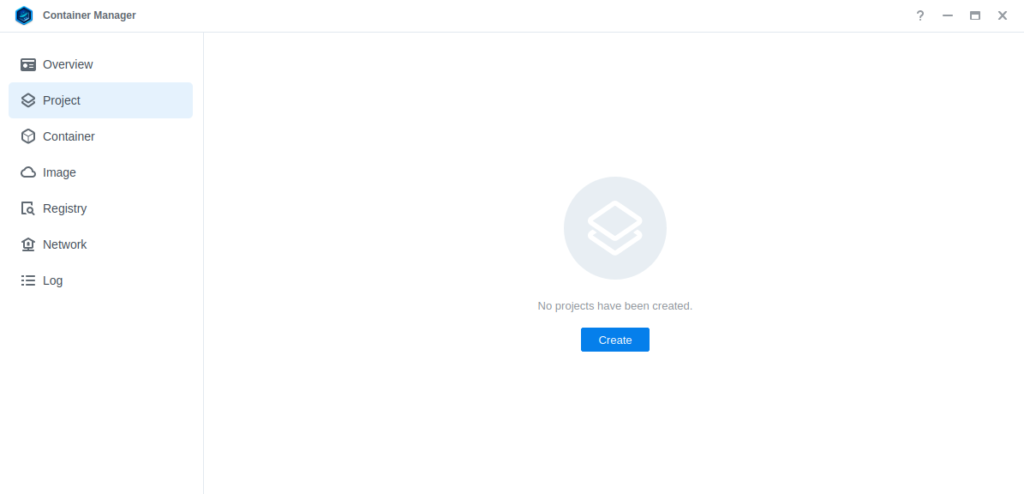
Next we are going to set up a ‘Project’ in Container Manager. Open up Container Manager and click on Project then on the right-hand side click ‘Create’.
In the next screen we will set up our General Settings, enter the following:
| Section | Setting |
|---|---|
| Project Name: | wg-easy |
| Path: | /docker/projects/wg-easy-compose |
| Source: | Create docker-compose.yml |
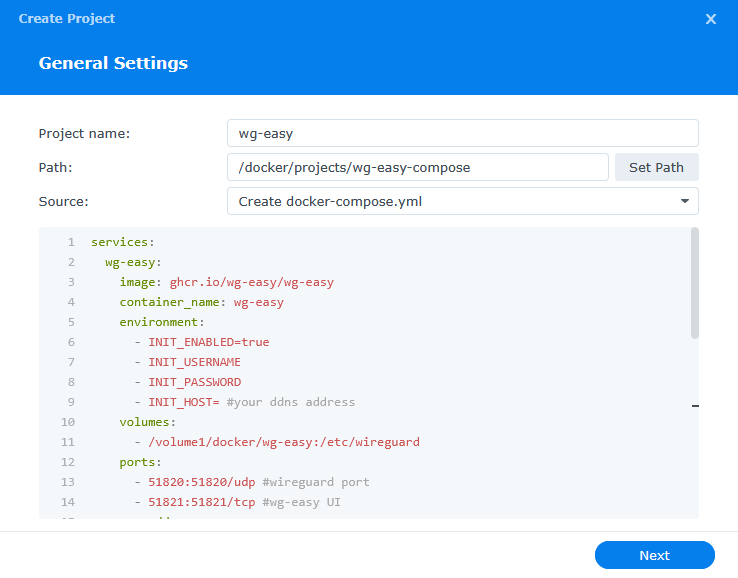
Next we are going to drop in our docker compose configuration, copy all the code in the box below and paste it into line ‘1’ just like the screenshot.
services:
wg-easy:
image: ghcr.io/wg-easy/wg-easy
container_name: wg-easy
environment:
- INIT_ENABLED=true
- INIT_USERNAME=
- PASSWORD_HASH= #your bcrypt hash
- WG_HOST= #your ddns address
volumes:
- /volume1/docker/wg-easy:/etc/wireguard
ports:
- 51820:51820/udp #wireguard port
- 51821:51821/tcp #wg-easy UI
cap_add:
- NET_ADMIN
- SYS_MODULE
sysctls:
- net.ipv4.ip_forward=1
- net.ipv4.conf.all.src_valid_mark=1
- net.ipv6.conf.all.disable_ipv6=0
- net.ipv6.conf.all.forwarding=1
- net.ipv6.conf.default.forwarding=1
restart: unless-stoppedEnvironment Variables
We are now going to amend some key variables which define how the WireGuard connection will be set up and behave, I have covered the key settings here to get you up and running. You can find a full list of variables on the WG-Easy GitHub.
| Variable | Value |
|---|---|
| INIT_USERNAME | Set a username for the web UI |
| PASSWORD_HASH | This is optional but recommended to enable a password login for the web UI – see the extra info below on how to do it. If you don’t want to enable this remove the line. |
| INIT_HOST | Change this to the DDNS address you set up in the previous steps |
Generating the web password
In order to enable the password for the Web UI you need to add a Bcrypt hash of your chosen password into the compose. Go to https://bcrypt.online/ to create the hash.
Enter the password in the ‘Plain Text Input’ box and then press the ‘Generate Hash’ button. Copy the generated hash next to the PASSWORD_HASH= line.
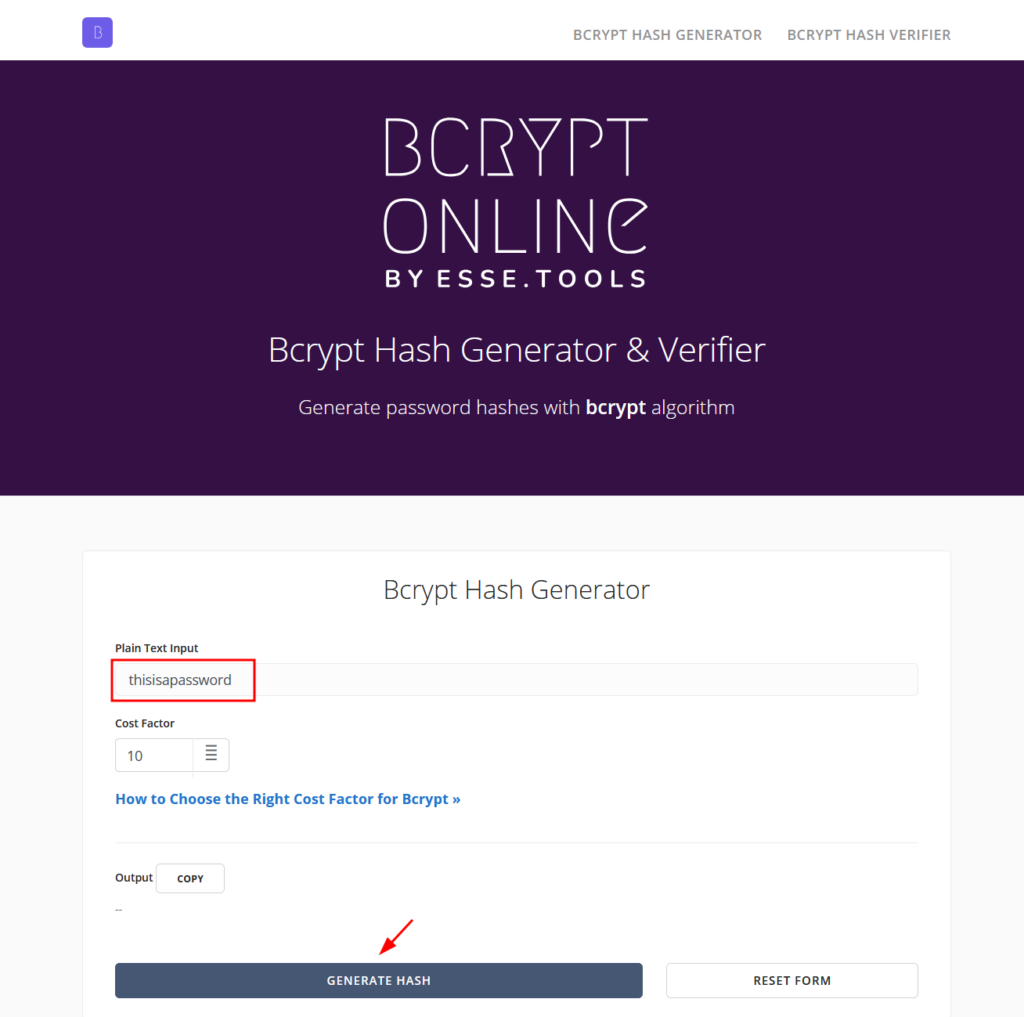
Finally you will need to slightly amend the $ signs in the hash to ensure it is read correctly from the compose by replacing any single $ to double $$ for example
$2y$10$Kpbc.6Ue5WClnHLxCxLOo.lNmJRg8inaNFu9tW03WaZpAGVLQRn76
becomes
$$2y$$10$$Kpbc.6Ue5WClnHLxCxLOo.lNmJRg8inaNFu9tW03WaZpAGVLQRn76
Once you have made the edits you can click ‘Next’
You do not need to enable anything on the ‘Web portal settings’ screen click ‘Next’ again.
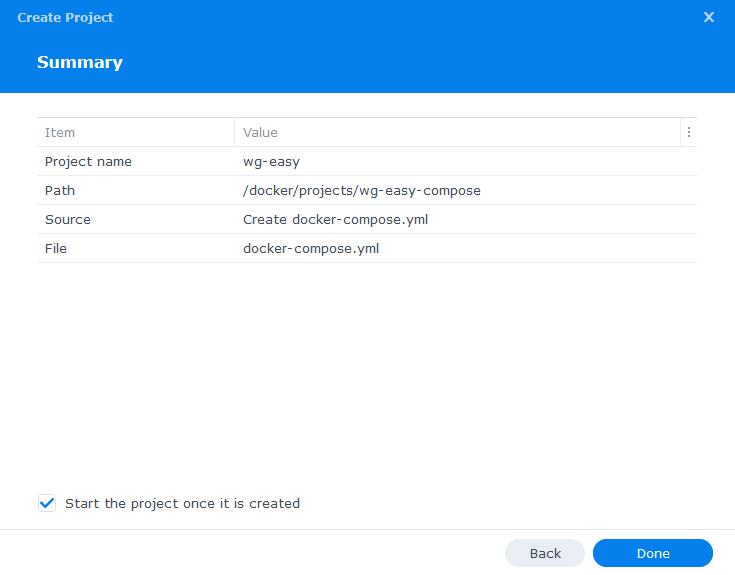
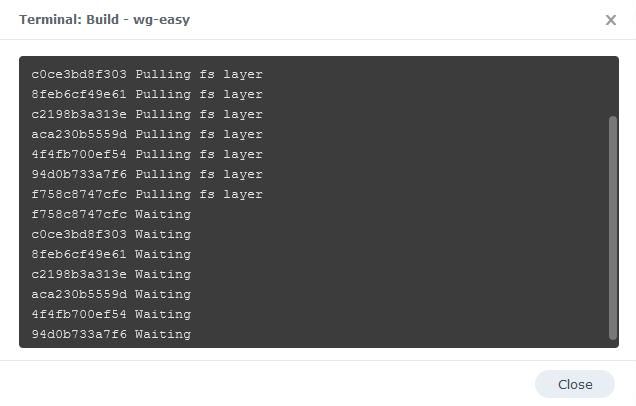
On the final screen click ‘Done’ which will begin the download of the container image and once downloaded it will be launched!
The image will now be downloaded and extracted. You should see ‘Code 0’ when it has finished.
Forward the WireGuard Port
Now the container is running it would be a good idea to head into your Routers settings and forward the port your set for the container (51820). Refer to the manual on how to do this, essentially the port will be forwarded to the NAS IP address.
Firewall Exceptions
(Skip if you don’t have the Firewall configured)
If you have the Synology Firewall enabled please see this additional guide for further info on exceptions and correct set up.
Client Set up
WireGuard Easy makes it super easy to set up each client. Go to the Web UI on your NAS IP port 51821
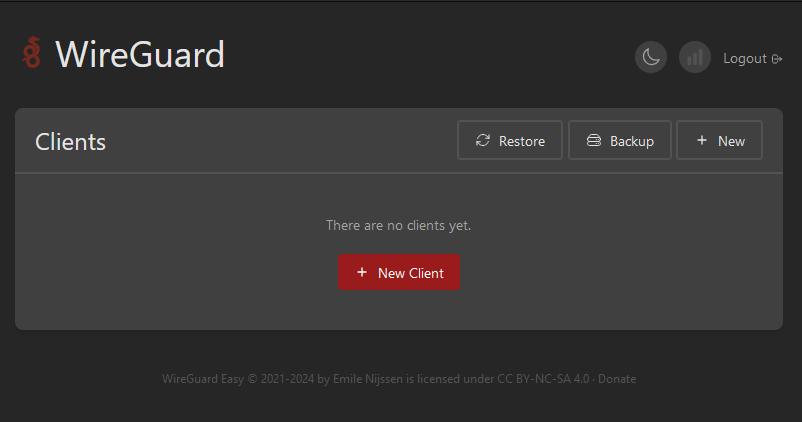
Simply click ‘New Client’ and the config details will be created automatically for you.
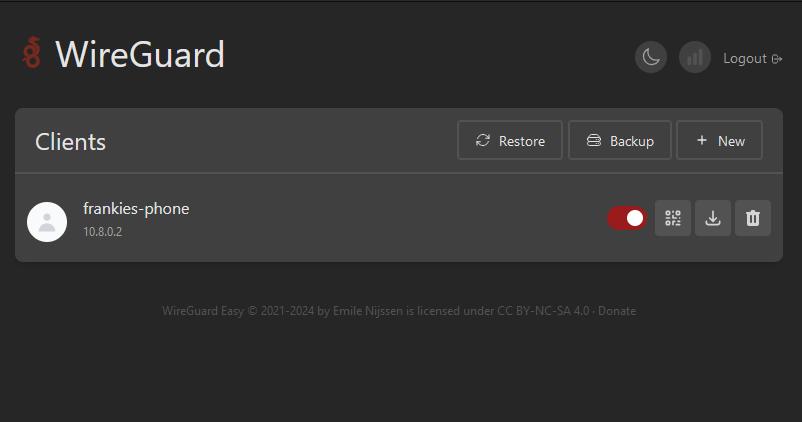
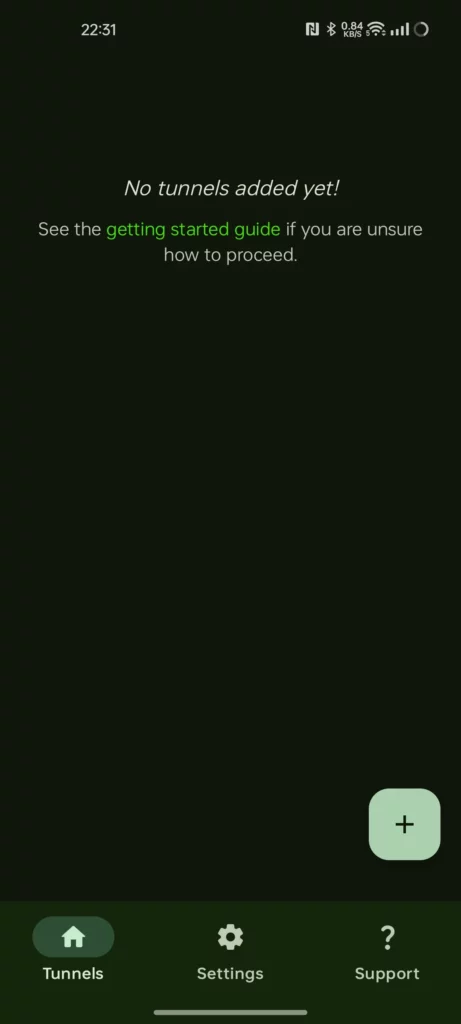
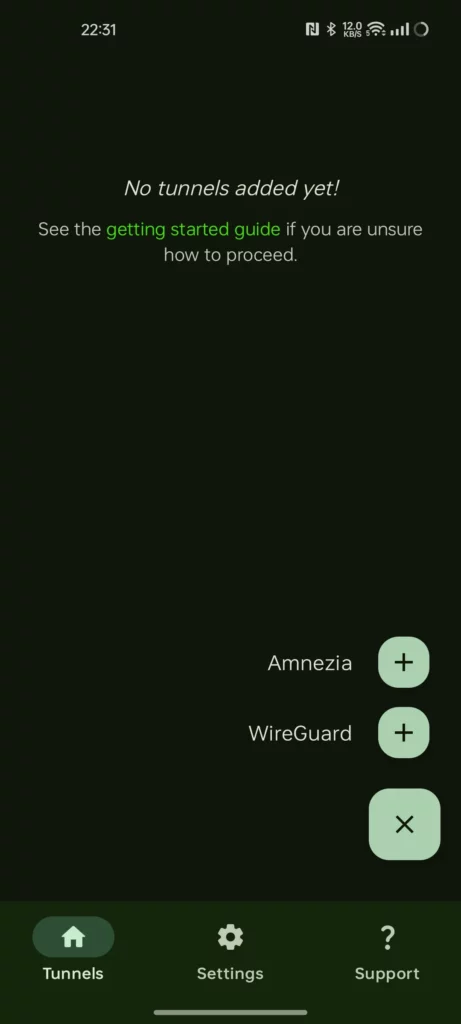
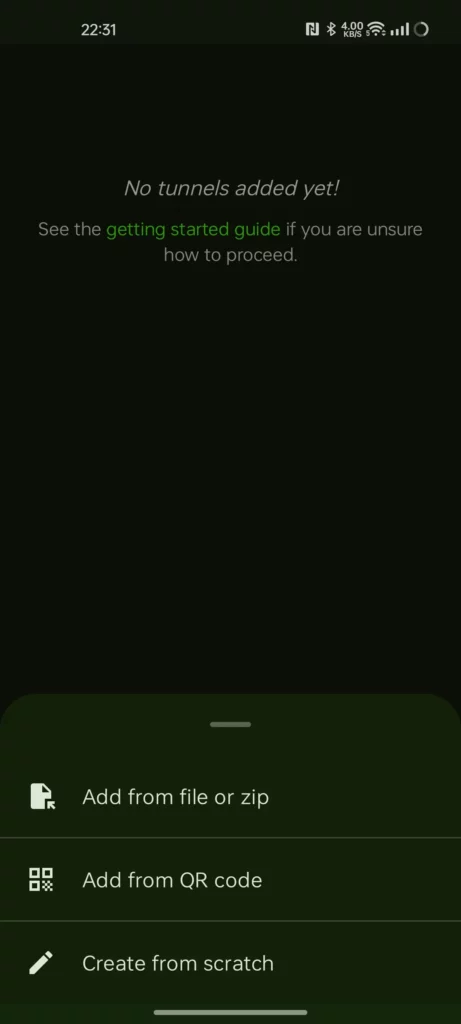
You have a couple of choices on how to add the config to your end device, for phones make use of a WireGuard app. For this guide I am using WG Tunnel on the Playstore, for iPhone users there is also a WireGuard app.
Open the App and Tap the + button in the bottom Right, then ‘WireGuard’ in the pop-up menu, then ‘Add from QR Code’. Scan the QR code from WG Easy.
You can now turn on the connection from within the app and when roaming away from home all your locally hosted services will just work like you are on Wi-Fi. Your internet traffic is also routed through the connection. I have found that battery impacts are negligible so leave the connection on 24/7.
Looking for some help, join our Discord community
If you are struggling with any steps in the guides or looking to branch out into other containers join our Discord community!
Buy me a beverage!
If you have found my site useful please consider pinging me a tip as it helps cover the cost of running things or just lets me stay hydrated. Plus 10% goes to the devs of the apps I do guides for every year.





Hi, thanks for the great write up. I have a question. I have this WG running for a while now on my Synology NAS. I can’t remember though if it is safe to update your DSM? Currently I am on DSM 7.2.1-69057 Update 5 and would like to update.
Does an update remove the kernel stuff we did to enable Wireguard?
Yeah DSM update is OK I just moved to 7.2.2 on my own box with no issues 🙂
Great, Thanks!
Hi,
Sorry im pretty new to all of this, If i’m using wireguard on my phone to access my jellyin on my NAS, can my isp or phone provider see what im doing or do i need https enabled with a ddns to connect to it.
Hi
The DDNS address is a TLS connection so just like any other website they see your DNS request to get the IP of the server (assuming It’s using the ISP DNS), and then the rest is over the WireGuard tunnel so completely hidden.
Hi Dr. Frankestein! Thank you for the guide. I’m considering using Wireguard on my Synology instead of OpenVPN, but I’m a bit concerned on installing the WireGuard Kernel Module. Is it safe? I mean, can we trust BlackVoid.club? I’m always reluctant to install unknown software from unknown sources or ones that are not official. I don’t have the knowledge or skill to see if they are doing something malicious on the background. I wish there was a way to do it without the kernel module, or for Synology to provide the kernel module, but since there isn’t I’m here asking if BlackVoid.club is trustworthy.
Thank you!
Hi perfectly valid question, its entirely down to you really, if this module were malicious I would of thought it would of been called out already, the source is available on Github with a number of contributers, meaning you can build from source if you didn’t want to use the pre-built spk’s
https://github.com/runfalk/synology-wireguard
Its all opensource so while that by itself makes no guarentees it does mean when other devs contribute they would see anything malicious going on. If I personally had any doubts I would not even put it forward as a solution.
I wouldn’t hold out much hope of Synology including it – they would ideally upgrade the Kernel which includes the WireGuard code (v5.6 onwards) my 1821+ is on 4.4.302+
Howdy its me again!
When I try to build the project, it returns “Error response from daemon: Get “https://ghcr.io/v2/”: net/http: request”
Hi Nick – Not sure why you are getting the error – unfortunately wgeasy is only available via the github repository not docker hub.
This is not an official image but try swapping the image line with this version its up to date.. image:leduong/wg-easy
That worked! Seems like I don’t have a good connection with ghcr.io. It could be be something with my DNS not being able to query it (using nextDNS). This happened before when I tried setting up homepage.
Sorry one more question.
How would I use the configs that come from the web ui and use it for the synology? Like use the synology itself as a client.
Oh you mean like a remote NAS back to the main NAS, you could use the previous image I was using in this guide in Client Mode, it should allow you to drop in the configs and the other NAS to connect right in..
https://github.com/linuxserver/docker-wireguard?tab=readme-ov-file#client-mode
No sorry. I meant the NAS that is running wg-easy. Using the same NAS as both the server and the client. How would I do that? Sorry for the confusion.
Im currently using tailscale but I want to replace it.
Can you give me an example of what you are intending to do sorry, I may be a bit slow at the moment as currently have a stinking cold…
So in the end of the guide you’ve shown how to add a phone as a client. Can I do the same on the NAS as well? On the same NAS thats running wg-easy.
From my understanding, right now the NAS is just a server. And I won’t be able to access it without installing the configs from wg-easy. So how would I be able to use the NAS as a client?
Oh I see, sorry. No need to do that at all. The NAS will be fully accessible as it is providing access to itself and any other local network devices via the server aspect. So when connected via mobile or any other device remotely you can access anything on the NAS just like you were in the same room.
Sorry for being difficult but what would the wg IP be for NAS then? Say I have 10.1.0.5/24 as the wg IP for my phone and I want to access jellyfin on the NAS with “:8096”, what would I use for for the wg ip address?
Not a problem, you would just use the normal NAS IP the Wireguard IPs are just purely between the two end points
Sorry for the stupid question…
I set up qBitTorrent and gluetun in docker on my Synology using your guide. Gluetun connects to my VPN using the WireGuard Balckvoid spk linked in the guide and all is good and more or less reliable.
On my Synology I also have the VPN Server package, and I use OpenVPN to remotely connect when I need to access files or containers on the NAS. Can I delete the Synology package and use this guide instead? Or since I’m already using WireGuard for glutetun, this guide becomes incompatible or improper?
Wireguard should be a little more modern, and I already have the app on my phone so I could ditch the openvpn one and fee some clutter. Also, the app seems more configurable.
Thanks for your awesome guides!
Hi not a stupid question at all – you can swap over to WireGuard if you like, they can work just fine together I use both here. The nice thing about WireGuard is if you open the port it won’t reply to anything other that you with the key, OpenVPN is a bit more obvious the port is there.
Hi Dr, I finally got the chance to try this guide but unfortunately the container is not starting up – it stops immediately and gets in a loop, the log says “cannot find device wg0 – This usually means that your host’s kernel does not support WireGuard!” among the rest.
Any idea why? Please see also my comment above.
My compose file: https://paste.drfrankenstein.co.uk/?e307984bc8986af1#ENsXtwS4S4dFHQsF96u44tsW2vi8QkpgNqPKUk5uWwTD
Thank you for even the smallest hint in the right direction!
Hey, yaml looks good. Double-check your WireGuard kernel module is running as that will stop the container starting up. You may need to repeat the steps in the ‘WireGuard Kernel Module (Required)’ section
Thank you vey much Dr., I have been too hasty – a simple uninstall&reinstall with a couple of reboots in-between seems to have fixed it! It’s amazing how fast it connects compared to OpenVPN, it’s literally instant!
Keep up the good work!