Important or Recent Updates
| Historic Updates | Date |
|---|---|
| Updated guide for Container Manager and using Macvlan | 14/05/2023 |
| Added a new section to ensure DSM continues having network access. | 02/06/2023 |
| Guide updated so you can choose between Macvlan or Bridge mode | 12/08/2023 |
| Added additional security option to the compose to restrict the container from gaining new privileges | 25/10/2023 |
| Fixed issues I introduced with the recent changes in my mission to make things more secure. It was so secure I broke it! Added the appropriate permissions/capabilities at start up for the container. | 29/10/2023 |
| Removed the requirement for the synobridge as this container can just use its own bridge, and added the Host network mode, so all three are a choice. | 28/01/2024 |
| Removed the WEB_UID and WEB_GID from the config to avoid issues with ID’s conflicting inside the container. I will update again once I have some time to work around this. | 03/04/2024 |
| Some minor amends to sync up the information across this guide and the AdGuard one | 01/08/2024 |
What is Pi-hole?
If you are looking to get advertising and tracking blocked across all the devices on your network a Pi-hole will have you covered. It’s a locally hosted Domain Name Server and uses block lists to stop adverts.
This guide will get you set up with Pi-hole and cover some basic initial settings, I recommend checking out the documentation for all the various features available.
Host vs Macvlan vs Bridge Network Modes
Host:
Host mode uses your NAS underlying network to run the containers network services, so it will be reliant on the NAS not using any of the required ports for the container. However, this makes it easy to set up, but you need to make sure no other service is using the required ports. All your clients will appear correctly as independent devices and stats.
Macvlan:
This gives you the benefit of Pi-hole having its own IP address on your network, all clients appear with their real IP addresses allowing you to assign specific rules and give you some nicer stats. However, one downside is that your NAS will not be able to use Pi-hole for DNS, due to the additional security features of Macvlan and its communication with its host. This is generally not an issue unless you wanted to use your Ad blocking with Tailscale.
Bridge Mode:
The main benefit of Bridge Mode will be the ease of setup however you will find that all clients on your network will appear under the same IP as the Bridge 172.20.0.1. This won’t impact ad blocking, but it will mean you can apply device specific rules etc.
Let’s Begin
In order for you to successfully use this guide you will need to check that your Router allows you to change your network DNS servers, this is usually found in the DHCP settings.
Please follow the two initial guides below to get a restricted Docker user set up, then come back here.
Folder Setup
Let’s start by getting some folders set up for the container to use. Open up File Station create the following.
/docker/projects/pihole-compose
/docker/pihole
/docker/pihole/dnsmasq.d
/docker/pihole/pihole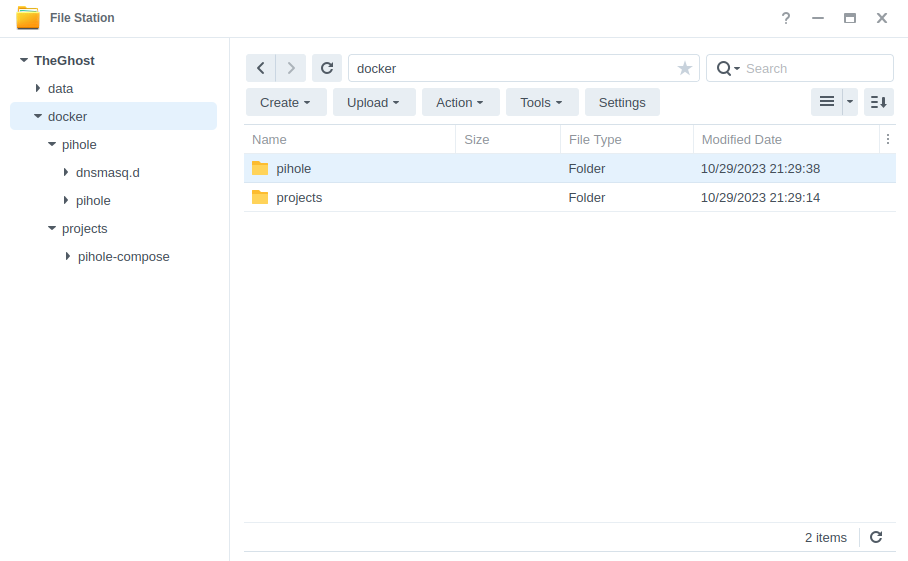
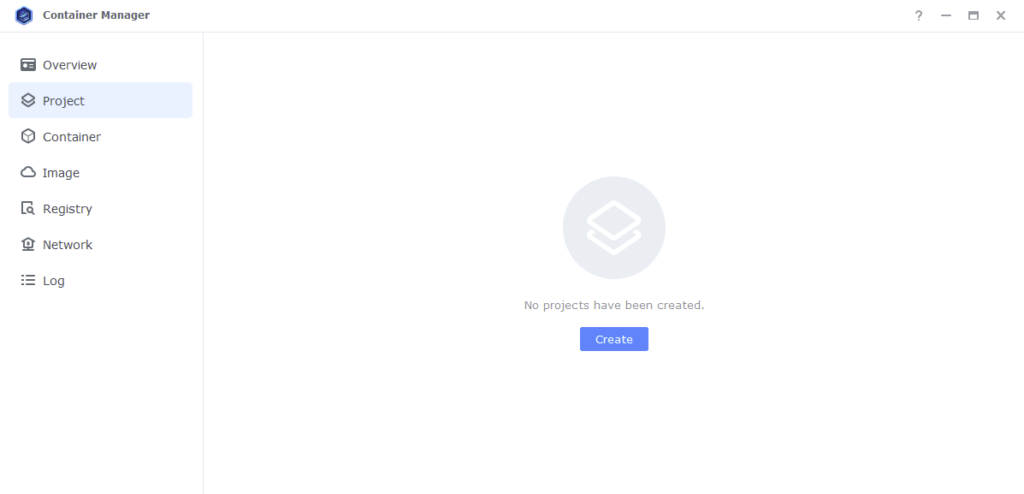
Container Manager
Next we are going to set up a ‘Project’ in Container Manager. Open up Container Manager and click on Project then on the right-hand side click ‘Create’.
In the next screen we will set up our General Settings.
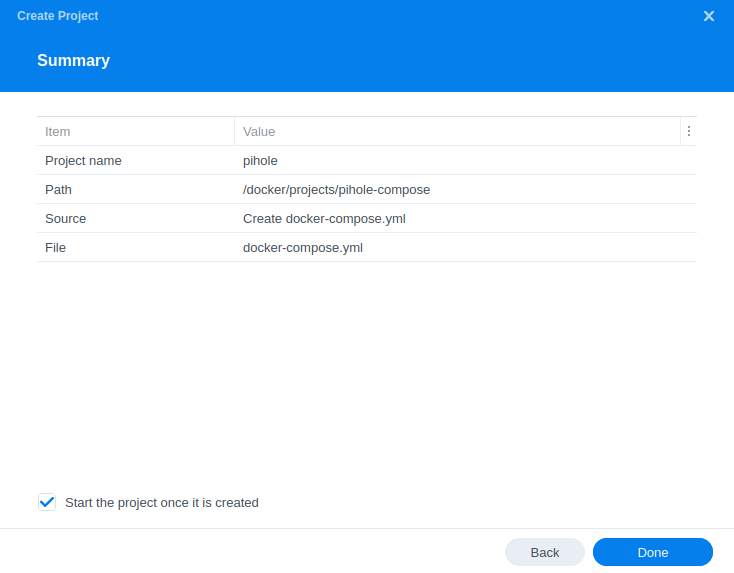
In the next screen we will set up our General Settings, enter the following:
| Section | Setting |
|---|---|
| Project Name: | pihole |
| Path: | /docker/projects/pihole-compose |
| Source: | Create docker-compose.yml |
Next we are going to drop in our docker compose configuration. You now need to decide if you are going to go with Macvlan or Bridge Mode and copy the appropriate compose from below and paste it into line ‘1’ just like the screenshot.
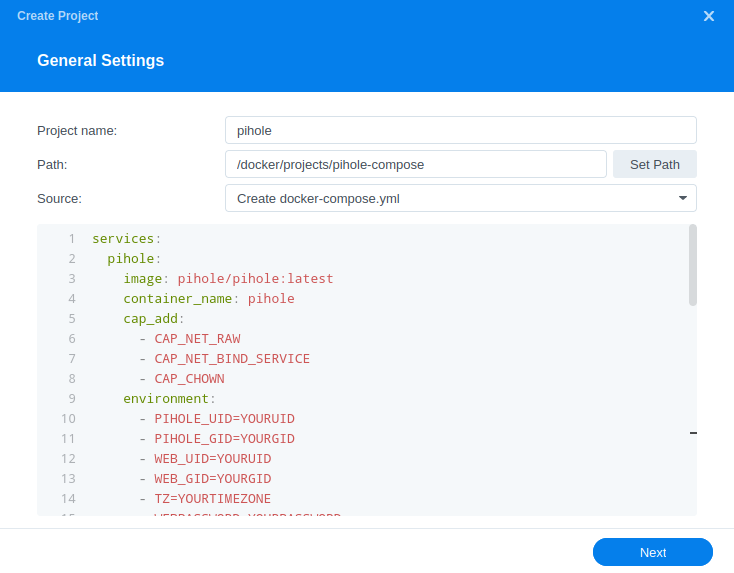
What on earth is a Docker Compose? Docker Compose allows us to define how Docker should set up one or more containers within a single configuration file. This file is yaml formatted and Container Manager uses the Projects feature to manage them.
Please note you will not be able to use Macvlan with a Bonded network connection e.g. ‘Bond0’. You will need to remove the bond in order to use this method.
Host
services:
pihole:
image: pihole/pihole:latest
container_name: pihole-host
cap_add:
- CAP_NET_RAW
- CAP_NET_BIND_SERVICE
- CAP_CHOWN
environment:
- PIHOLE_UID=1234 #CHANGE_TO_YOUR_UID
- PIHOLE_GID=65432 #CHANGE_TO_YOUR_GID
- TZ=Europe/London #CHANGE_TO_YOUR_TZ
- WEBPASSWORD=YOURPASSWORD
- DNSMASQ_LISTENING=local
- WEB_PORT=8000
- DNSMASQ_USER=pihole
- FTLCONF_LOCAL_IPV4=YOURIPV4ADDRESS
volumes:
- /volume1/docker/pihole/dnsmasq.d:/etc/dnsmasq.d
- /volume1/docker/pihole/pihole:/etc/pihole
network_mode: host
restart: unless-stoppedMacvlan
services:
pihole:
image: pihole/pihole:latest
container_name: pihole-macvlan
cap_add:
- CAP_NET_RAW
- CAP_NET_BIND_SERVICE
- CAP_CHOWN
environment:
- PIHOLE_UID=1234 #CHANGE_TO_YOUR_UID
- PIHOLE_GID=65432 #CHANGE_TO_YOUR_GID
- TZ=Europe/London #CHANGE_TO_YOUR_TZ
- WEBPASSWORD=YOURPASSWORD
- DNSMASQ_LISTENING=local
- WEB_PORT=8000
- DNSMASQ_USER=pihole
- FTLCONF_LOCAL_IPV4=YOURIPV4ADDRESS
volumes:
- /volume1/docker/pihole/dnsmasq.d:/etc/dnsmasq.d
- /volume1/docker/pihole/pihole:/etc/pihole
networks:
macvlan:
ipv4_address: 192.168.0.129
restart: always
networks:
macvlan:
name: macvlan
driver: macvlan
driver_opts:
parent: eth0
ipam:
config:
- subnet: "192.168.0.0/24"
ip_range: "192.168.0.254/24"
gateway: "192.168.0.1"Bridge Mode
services:
pihole:
image: pihole/pihole:latest
container_name: pihole-bridge
cap_add:
- CAP_NET_RAW
- CAP_NET_BIND_SERVICE
- CAP_CHOWN
environment:
- PIHOLE_UID=1234 #CHANGE_TO_YOUR_UID
- PIHOLE_GID=65432 #CHANGE_TO_YOUR_GID
- TZ=Europe/London #CHANGE_TO_YOUR_TZ
- WEBPASSWORD=YOURPASSWORD
- DNSMASQ_LISTENING=local
- WEB_PORT=8000
- DNSMASQ_USER=pihole
- FTLCONF_LOCAL_IPV4=YOURIPV4ADDRESS
volumes:
- /volume1/docker/pihole/dnsmasq.d:/etc/dnsmasq.d
- /volume1/docker/pihole/pihole:/etc/pihole
ports:
- 53:53/udp
- 8000:8000/tcp
restart: unless-stoppedWe are now changing some settings this applies to all versions of the YAML above.
| Section | Explanation |
|---|---|
| PIHOLE_UID= | This UID is the one you obtained when setting up your dockerlimited user in the earlier guide at the start of the page. This tells Pi-hole to run under this user rather than root and gives it access to the folders we created. |
| PIHOLE_GID= | As per the above this line will be the GID you obtained earlier. |
| TZ= | You will need to change this line to your own timezone code – you can find the correct list of ones to use on wikipedia.org/wiki/List_of_tz_database_time_zones |
| WEBPASSWORD= | Change this to the password you would like to use for the Web UI |
| FTLCONF_LOCAL_IPV4= | If you are using the Bridge Mode this line will be the IP address of your NAS If you are using MACVLAN Mode this line will be the same as line 25 when you do that part below. |
If you are setting up the Bridge or Host versions you can now press next and jump ahead in the guide to Web portal settings for MACVLAN continue on below.
Settings Amendments for the Macvlan
OK we now need to make some further edits to the compose and sort out DNS for DSM
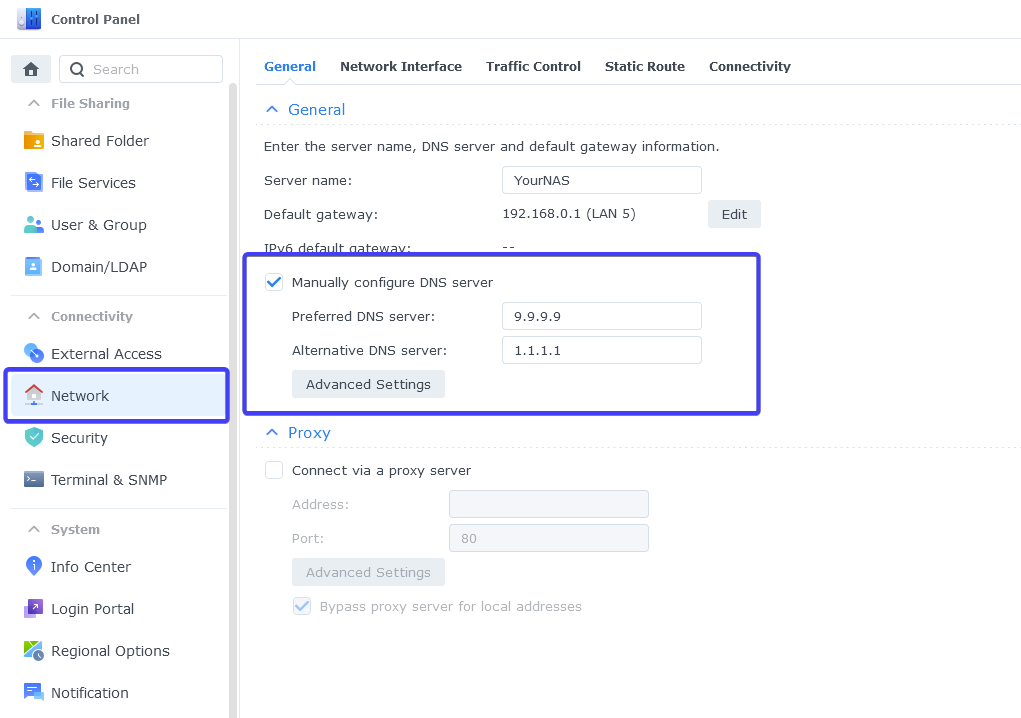
External DNS for DSM
Containers on a Macvlan cannot be accessed by the host they reside on (without network changes under the hood), this mean DSM cannot use Pi-hole for its own DNS requests. It’s better to put DSM on an external DNS provider to avoid it having any issues connecting to the Internet if your Pi-hole is down.
Go into the DSM Control Panel > Network and then in the ‘Manually configure DNS server’ set two good quality DNS providers such as Quad9 9.9.9.9 and Cloudflare1.1.1.1
Now you can make some edits to the compose information before moving on
| Section | Explanation |
|---|---|
| ipv4_address: 192.168.0.122 | Change to the IP address you want to use for the container. Make sure this is available and not in use by another device on your network. Don’t forget to go back up and change line 15. |
| parent: eth0 | This defines the network interface the container should use, I have used eth0 which will be the first Ethernet port on your NAS. If you want to use a different port change it accordingly. Note! If you have Virtual Machine Manager installed change this to ovs_eth0 |
| subnet: “192.168.0.0/24” | We need to change this in line with your networks’ subnet – in the example I have used 192.168.0.0/24. The super quick way to work out what to use is just take the IP of your NAS and change the final digit before the /24 to 0 |
| ip_range: “192.168.0.254/24” | This has to be changed to the highest available IP address within the range of your subnet. Again if your network is in the 192 range the final number used from the subnet above can be changed to 254 and added to this section. |
| gateway: “192.168.0.1” | This will be the IP address of your Router/Gateway/DHCP Server |
Once you have made the edits you can click ‘Next’
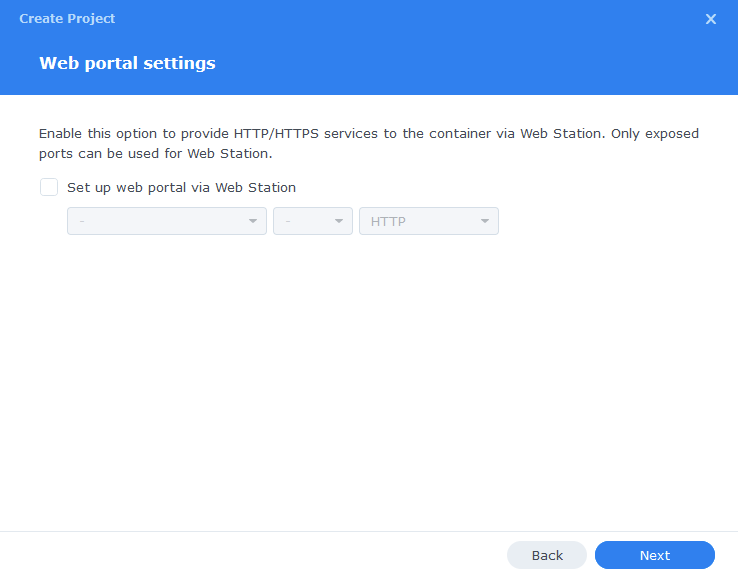
Web portal settings
You do not need to enable anything on the ‘Web portal settings’ screen click ‘Next’ again.
On the final screen click ‘Done’ which will begin the download of the container images and once downloaded they will be launched!
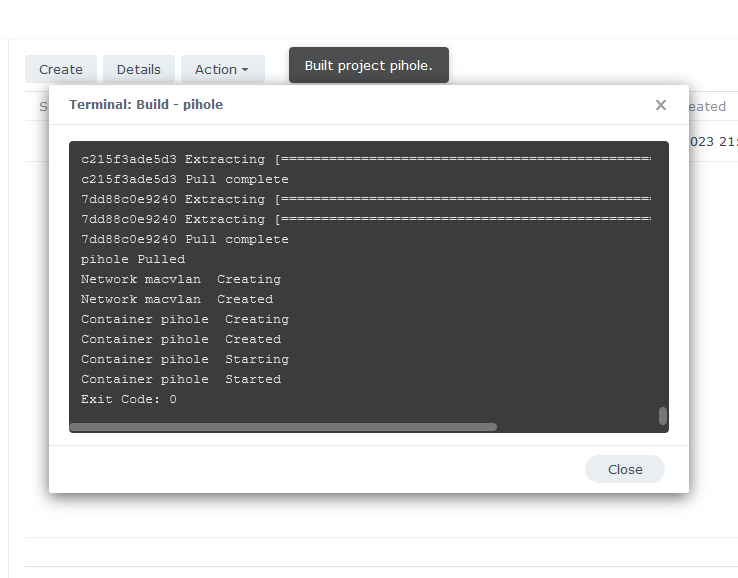
The image will now be downloaded and extracted. You should see ‘Code 0’ when it has finished.
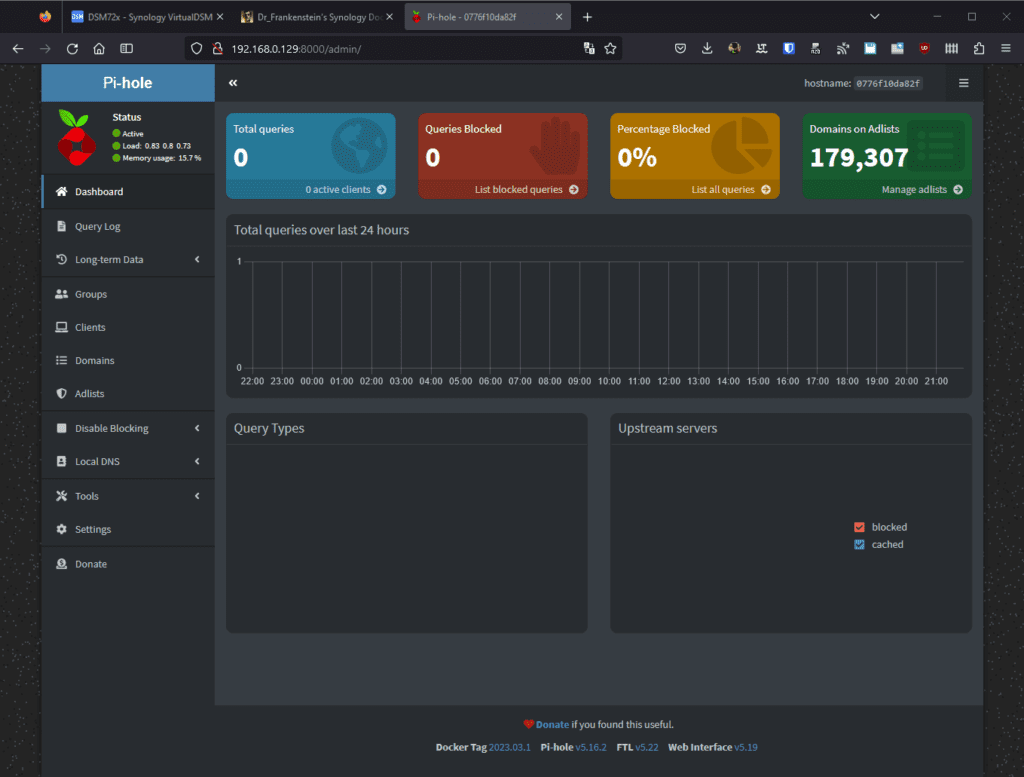
You will now see your Pi-hole running and should have a green status on the left-hand side.
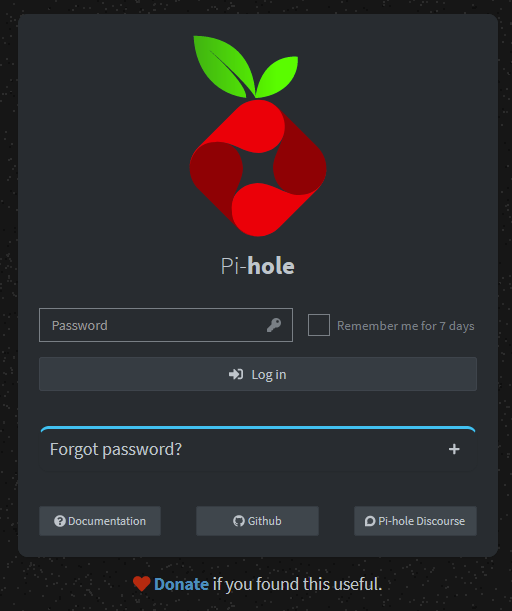
The web interface will now be available via the below.
Macvlan = the IP you specified in the compose followed by the port :8000/admin/login.php
OR
Bridge or Host = Your NAS IP followed by the port :8000/admin/login.php
You can access the UI with the password you specified in the compose.
Update your Router DNS
Now you need to add the appropriate IP address to your router depending on which method you used to set up Pi-hole
Bridge or Host = NAS IP
MACVLAN=The address you chose for the container on the line ‘ipv4_address:’
It can take some time for all of your devices to move over the new DNS settings so be patient, and you will gradually start to see your stats begin to start.
Also note as we are not using Pi-hole as the DHCP server you will not be able to see the names of the devices in the statistics just their IP addresses.
That’s it!
FAQ:
What ports does Pi-hole use?
| Port | Protocol | Used For |
|---|---|---|
| 53 | TCP/UDP | DNS |
| 67 | IPv4 UDP | DHCP – Only used when the ipv4 DHCP server is enabled. |
| 547 | IPv6 UDP | DHCP – Only used when the ipv6 DHCP server is enabled. |
| 8000 | TCP | For the WebUI |
Looking for some help, join our Discord community
If you are struggling with any steps in the guides or looking to branch out into other containers join our Discord community!
Buy me a beverage!
If you have found my site useful please consider pinging me a tip as it helps cover the cost of running things or just lets me stay hydrated. Plus 10% goes to the devs of the apps I do guides for every year.




Hi,
great guides.
I wonder if anyone has a guide to enable IPV6 Support ?
regards,
Tim
Thanks for the excellent guide. I don’t suppose that you have any pointers for adding Unbound to the pi-hole configuration?
Have had a few requests for this, let me see what I can cook up as would need to set it up here in order to then support.
Excellent tutorial! I am preparing to install pi-hole in bridge mode (once all configured, I will be setting up Tailscale as per your Tailscale tutorial). I have Cloudflare DNS nameservers configured in Synology and router. At the end of your tutorial you say “Now you need to add the appropriate IP address to your router depending on which method you used to set up Pi-hole”. I will be in Bridge mode and understand its the NAS IP but where and why am I adding the IP address in router settings? (Sorry for the basic question and thank you in advance).
Hey, the ip in the router is so all devices on your network then use pihole for their dns lookups, you would then use based on your preferences put the Cloudflare dns into pihole for its upstream lookups. I would keep the NAS on external dns just to ensure it always has Internet access for if the PiHole is down for updates etc
Thanks! I’ve pointed Primary DNS on router to NAS IP and Secondary DNS to Cloudflare. Left DNS on NAS as Cloudflare and switched to Cloudflare in PiHole. All seems good now. Onto, Tailscale now!
has anyone have pihole working with DoT on synology?
what i want to achieve is setting the private dns in android to my own pihole.
i found this post
https://blog.svarun.dev/configure-pi-hole-with-dns-over-tls-private-dns
but changing the nginx on synology bascily get overriden everytime.
any ideas?
I know this is not DOT, but you can use DNS over HTTPS (DOH) using the quad9 address of https://dns.quad9.net/dns-query
https://quad9.net/news/blog/doh-with-quad9-dns-servers/
I am trying to set this up so that I can use Pi-hole set up via the Macvlan guide here with my VPN, so I can get Pi-hole working externally. When I connect to my NAS with OpenVPN, it doesn’t use the Pi-hole. Furthermore, I’m trying to link to the assigned IP address of the webpage with a reverse proxy, but it is unable to resolve the link. I know next to nothing about Macvlan, so could you provide some insight into why this may be occurring, if possible? Thanks you!
It sounds like you are trying to access the PiHole services from the NAS with a macvlan the service is not accessible from the host machine. So you would have to run pihole in normal bridge mode and then the NAS can use it for vpn / proxy etc.
Moving to bridge mode did indeed fix it! I’m sad I’ll lose the individual clients but configuring it through my router is more convenient anyways.
I have been trying to get a bridge between the container and nas working that doesn’t involve getting into ssh and editing things, if I even get it working I will be updating the guide. I have found that once pihole is working you will rarely touch it again.
For what it’s worth, this guide might be worth reviewing. I’ve got my setup finally working with all devices, so I’m not going to try touching this quite yet haha. But if this were to work in a way such that I could use pi-hole and also enable DHCP through pi-hole, I’d pursue it!
https://tonylawrence.com/posts/unix/synology/free-your-synology-ports/
On MACVLAN you can enable DHCP but just be aware that you will need to always make sure the NAS is set at a manual IP address as it won’t be able to access the DHCP server on PiHole. (due to aforementioned isolation)